Tem Used to Describe an Attacker Watching a Potentioal Target
Answer the question posting your initial response minimum 250 Words. The attackers first goal is to identify potential targets for their mission.
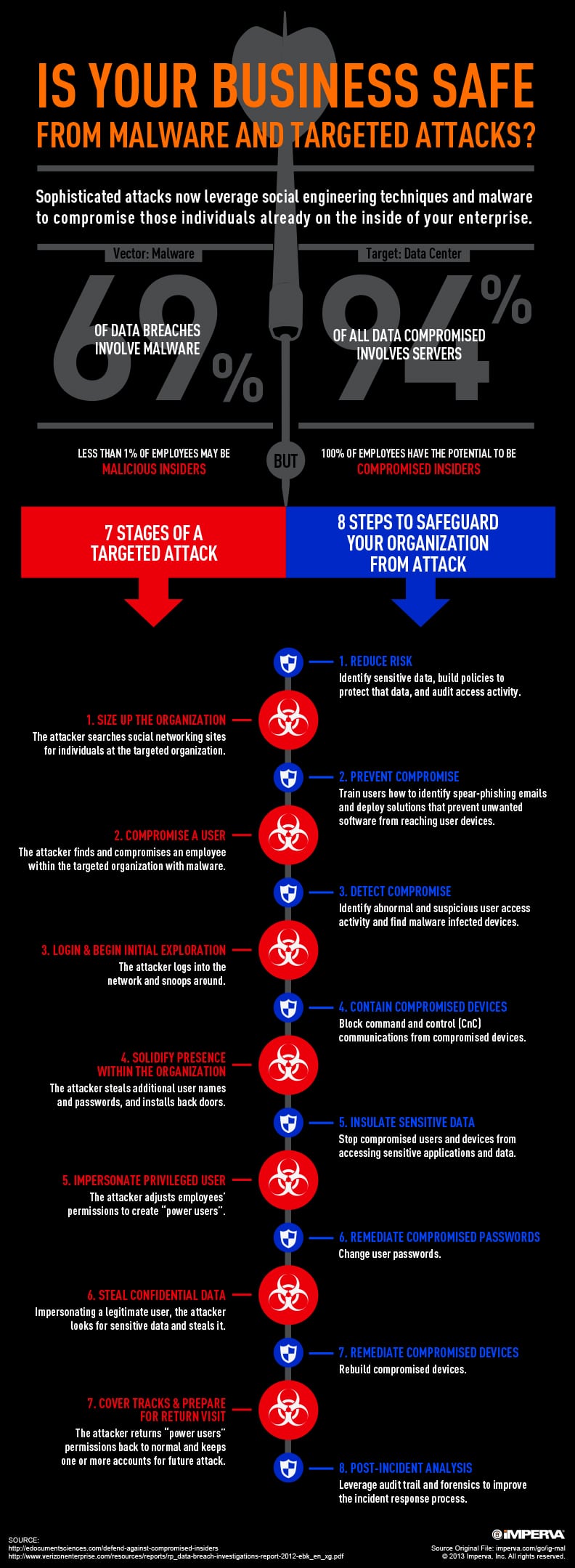
7 Stages Of An Advanced Targeted Attack Resource Library
Attackers are often motivated by financial gain access to sensitive information or damage to brand.
. Vishal Dhupar MD Symantec. Added 86 days ago6152021 125413 PM. September 30 2020 postadmin Leave a comment.
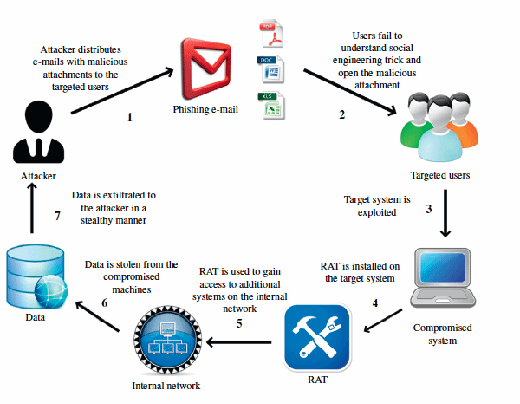
Log in for more information. Social engineering or psychological manipulation. Every endpoint is a potential target for attackers.
Stalking is a term used to describe an attacker watching a potential target with intent of harming it. 100 original work no plagiarism. This preview shows page 2 - 5 out of 8 pages.
What is the top method an attacker might infect a target. APA format and references. Describe how an attacker could use a sniffer.
Describe how an attacker could use DoS of attack to target both APs and clients. Every endpoint is a potential target for attackers. Social engineering or psychological manipulation.
And then ran mimikatz which resulted in domain admin credential disclosure. 100 original work no plagiarism. The attacker then ran the following command net view ComputerNameAdmin.
O a Do some scanning using the connected command Ob Use the tracert command Oc Do a host discovery by sending ping. What term is used to describe a potential attack on a system 2 out of 2 points. What is the top method an attacker might infect a target.
Please utilize the items described in the lessonresources or research conducted. This command enabled the attacker to see all shares. Which of the following types of attack will the attacker MOST likely conduct next.
Added 53 days ago5222021 44317 PM. With an increasing number of security threats lurking in the backyard of todays mobile devices their safety is at stake. Log in for more information.
Which of the following can he use in order to determine whether the potential target is connected to the network and is responsive. School University of the Cumberlands. Answer the question posting your initial response minimum 250 Words.
Describe how an attacker could use the Wi-Fi pineapple recon scan data to target unassociated clients with the WiFi Pineapples Allow Associations Capture SSIDs to Pool and Broadcast SSID Pool capability. Social engineering or psychological manipulation. The screenshot of the recon scan is.
Stalking is a term used to describe an attacker watching a potential target with intent of harming it. Describing An Attacker. Please utilize the items described in the lessonresources or research conducted on the web to ensure your post contains the following.
Log in for more information. Have you been attacked by someone that got away. An attacker is preparing an attack.
Describe how an attacker could use DoS of attack to target both APs and clients. September 30 2020 postadmin Post in Uncategorized. Stalking is a term used to describe an attacker watching a potential target with intent of harming it.
Course Title EMSISS ISOL 531. October 17 2012 by Nicole Gallow. Or do you know someone that has been.
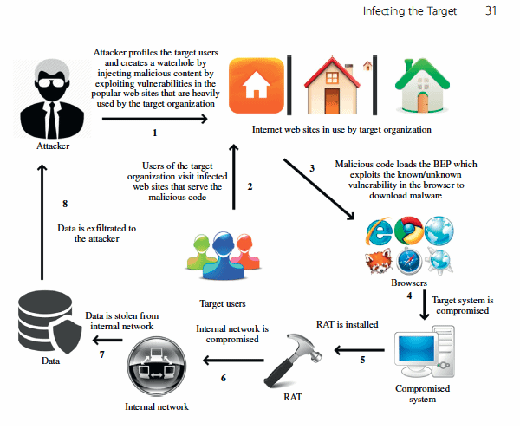
He got the IP address of a potential target computer. They start out with an attacker scoping out a potential target and gaining as from CYBERSECUR 610 at University of Maryland College Park. What term is used to describe a potential attack on a.
Describe how an attacker could use DoS of attack to target both APs and clients. Subparagraph a uses the word serious hindering or interruption as a constituent element of the offence in order to describe the effects of such an attack. Overview of Future Skills and Cyber Security.
Well this is for you not only to read and learn from but to SHARE the knowledge with your friends and family. This question hasnt been solved yet Ask an expert Ask an expert Ask an expert done loading. The real target is the sensitive customer data.
If you or a loved-one was ever attacked and you needed to explain your attackers physical features to the. Describe how an attacker could use a sniffer. With an increasing number of security threats lurking in the backyard of todays mobile devices their safety is at stake.
Pages 8 Ratings 54 24 13 out of 24 people found this document helpful. Symantec aspires to provide security storage and systems management solutions to secure and manage information against risks completely and efficiently. APA format and references.
Vishal Dhupar managing director. Hacking via the Internet Correct Answer A. Added 100 days ago5222021 44317 PM.
An attacker accessed a target host with standard user credentials. Symantec aspires to provide security storage and systems management solutions to secure and manage information against risks completely and efficiently. EurLex-2 Attack Sometimes used to describe an aggressive or provocative variation such as the AlbinChatard Attack or ChatardAlekhine Attack the Fried Liver Attack in the Two Knights Defense and the Grob.
So what happens in each phase of the attack. Describe how an attacker could use a sniffer.
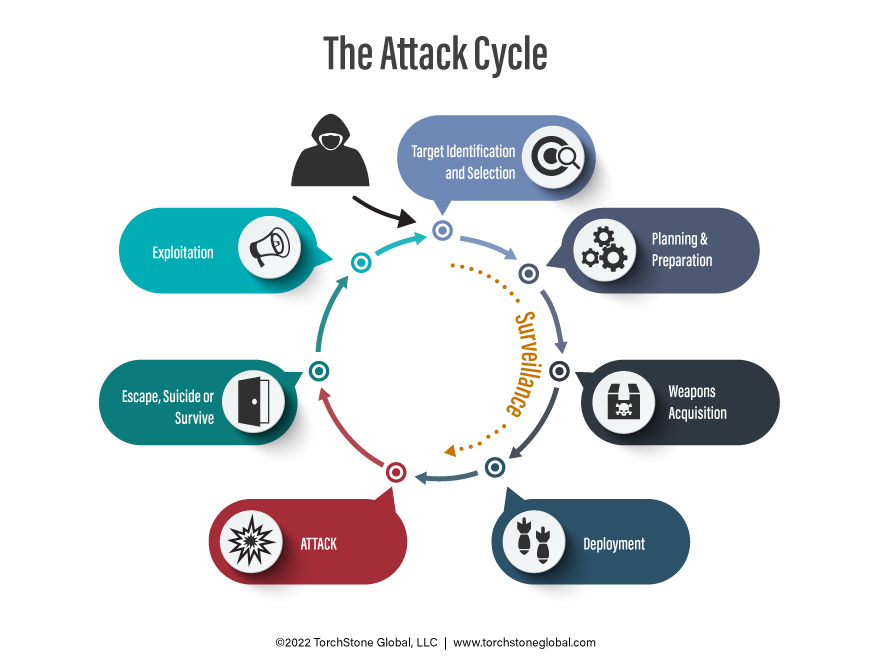
Exploiting Vulnerabilities In The Attack Cycle Torchstone Global
Comments
Post a Comment